The blockchain and cryptocurrencies
New technologies have enabled individuals to organise among themselves without having to go through an intermediary. This is true of the internet, which everyone uses but has no supervisory authority. Like the internet, the blockchain is a technology for storing and sharing secure information.
But what is the blockchain really? And how does it work?
From hashing to mining and blocks to cryptocurrencies, read on to find out more!
THE BLOCKCHAIN
A brief history
The architecture underpinning blockchain technology was first described in 1991 by Stuart Haber and W. Scott Stornetta, who developed a system for time-stamping digital documents to prevent them from being falsified or backdated.
In 1992, the “Merkle tree”, also known as the “hash tree”, was added to the system, making it more effective by enabling the grouping of several documents in a single block through the use of cryptographic functions. We will look at this in more detail later.
At the time of the economic crisis in 2008, a person going under the pseudonym of Satoshi Nakamoto (their real name remains unknown to this day) published a white paper specifying the functioning of a decentralised, peer-to-peer digital currency called “bitcoin”. To make the digital currency work, Nakamoto invented an IT protocol that would enable users to check the history of bitcoin transactions. It is this protocol that we call the blockchain.
Hashing and the Merkle tree
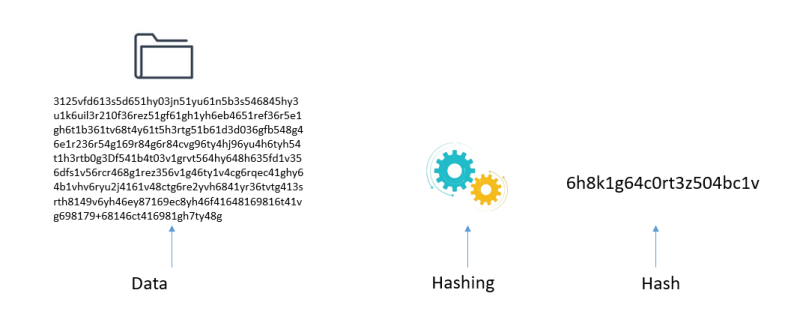
Hashing is a mathematical algorithm used to convert an object of arbitrary size, such as a text, file or video, into a chain of fixed length. We used the word “hash” because it is unique.
The algorithm used for bitcoin is SHA-256 (SHA being short for Secure Hashing Algorithm).
The hash length is 256 bits, or 64 characters.
Example of hashing: the table below shows the inputs and outputs after a hashing operation. As you can see, regardless of the initial data length, the output is a text in hexadecimal format of 64 characters.
The slightest change in the initial text completely modifies the hash (see the text in red).
The hash function works on a one-way basis only. You can obtain a hash from a set of data, but you cannot retrace a set of data from a known hash.
Did you know? A host of online tools exist for hashing content
For example: https://xorbin.com/tools/sha256-hash-calculator
The Merkle tree
A Merkle tree is a structure linking all transactions and grouping them into pairs to obtain a “Merkle root”.
Each Merkle root is present in the header of each block. It represents the condensed digital hash of all the information in the block.
So what exactly is the blockchain?
In practical terms, it is a decentralised database – in short, a digital accounting register – shared between its various users, with no central authority, and containing the history of all the exchanges made since its creation, which everyone may access. Data entry is irreversible and thus cannot be falsified.
Unlike a conventional database, the information is stored in blocks that are then linked together. Once a block is approved, you move on to a new block.
Various types of information can be stored in a blockchain, but so far most of it concerns transactions.
The decentralised database is stored not on a central server but on several computers – and thus a large number of servers – called network nodes. In the event of a server hack or loss, the database is protected because it continues to be stored in the other networks.
Several blockchains exist:
- Public blockchains, open to everyone, including Bitcoin, Ethereum, Dashcoin and Monero.
- Private blockchains (consortium or permitted), access to which is limited to a certain number of users, including R3 (banks) and B3i (insurance).
Transaction types
Contrary to what might be thought, the blockchain is not simply for transmitting cryptocurrencies (see cryptocurrencies). Several types of transaction may be made:
- An exchange of digital assets (virtual goods), such as security token offerings (STOs), ownership deeds and other documents
- Digital contracts (known as smart contracts)
- Votes
Important: all transactions are recorded on pages before becoming blocks.
Examples of the information provided in a bitcoin transaction:
- Transaction time and date
- Sender
- Beneficiary
- Amount
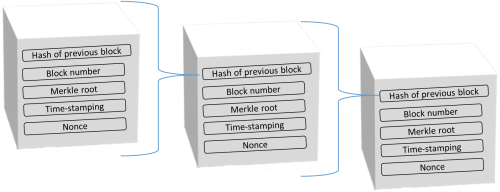
Blocks
As seen earlier, the blockchain is made up of blocks containing hundreds of transactions, one being added to another to form a chain. Each block of transactions, unique and time-stamped, serves as a foundation for the next block. A new block is formed roughly every ten minutes.
Each block thus contains:
- The number of the block
- The hash of the previous block
- Information on transactions
- The “hash” of the new block
- A time stamp
As with a fingerprint, each hash is unique.
Approving blocks
Each network node receives and records the new transactions in a waiting list.
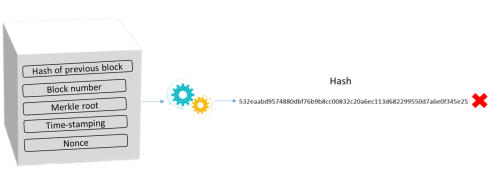
To propose your own “waiting” list as the new block, each node must first detect the encryption key (a random number referred to as a “nonce”). This is known as “mining”. To that end, an IT problem depending on the block must be solved (cryptography techniques). The first to succeed may propose their block to other people, who check that it is correct. If so, everyone inscribes this key on the page. The block may then be added to the blockchain.
As finding a key calls for substantial computing power, the person who finds it is rewarded with a fee.
To limit the creation of blocks, some blockchains (including the bitcoin blockchain) make mining difficult by asking miners to solve complex mathematical problems requiring considerable computing power. This is known as the “proof of work” concept.
Miners are then asked to find a nonce that, combined with the other information in the block, supplies a hash of the block featuring certain characteristics. This may involve finding:
- a hash that is inferior to a target difficulty
- or that the block hash starts with a certain number of zeros (the bitcoin network).
Example :
A random figure is attributed to the nonce. Hashing produces a suite of 46 characters.
=> For the bitcoin network, this hash will not be valid because it does not start with several zeros.
As a result, the miner has to “play” on the value of the nonce until he or she comes up with a block hash starting with 000000.
***
Reminder: The use of the blockchain is not limited to the use of cryptocurrency. The blockchain is used in more globally active cryptos, including cryptocurrency, naturally, as well as shares and bonds, and all types of new digital assets, such as non-fungible tokens, that can be considered as types of property.
But the main focus of this article is cryptocurrency.
The functioning of the blockchain requires the use of tokens that can be digitally transferred between two people. The use of tokens depends on the properties attributed to them.
Various types of token exist:
- Currency tokens, used for making payments.
- Utility tokens, representing rights to goods or services. Their use remains limited.
- Security tokens, linked to offers of securities (shares, bonds, etc.). These activities are supervised via a considerable number of existing or pending national regulations (the PACTE Law in France) together with proposals for the new Mica regulations and the pilot scheme in Europe.
Let’s take a look at the most well-known tokens, currency tokens. But to do so, we first need to define cryptocurrency.
***
CRYPTOCURRENCIES
What is a cryptocurrency?
Definitions vary considerably and are not necessarily aligned, depending on the regulations and laws in question.
According to the French consumer institute, Institut National de la Consommation (INC), a cryptocurrency is “a virtual currency based on an IT protocol of encrypted and decentralised transactions referred to as the blockchain”.
Put more simply:
A cryptocurrency is a virtual currency based on a system that protects data using keys or secret codes. This is the principle of cryptography.
It uses blockchain technology.
It is created with computer coding.
It is exchanged on a peer-to-peer basis, with no central authority, i.e. no supervising entity or body. Transactions are approved by a set of people (miners).
It has no physical medium, unlike coins or notes.
It is not considered as legal tender and is indexed neither on conventional currencies nor gold. Its price depends solely on supply and demand, hence its speculative aspect.
A variant exists called “stablecoin”, a type of cryptocurrency with a stable value, i.e. with extremely low price volatility.
Several cryptocurrencies exist. The top five in terms of market value (over $10 billion) are as follows:
- Bitcoin
- Ethereum
- Tether
- Ripple
- Litecoin
Some 2,871 cryptocurrencies were in circulation worldwide in 2019. source
Their prices can be tracked on a number of sites.
Here is a look at the prices of the main cryptocurrencies.

Price at 26/03/2021
Source : https://coin24.fr/cours/
Note: Virtual currencies can now be used to buy consumer goods, but unlike the euro, which has legal-tender status, they are not accepted everywhere. Nothing obliges a website or shop to accept them.
Did you know? Physical bitcoins have been minted. The most well-known is “casascius”, created by Mike Caldwell in 2011, in circulation until the US government prohibited all new coins in 2013. The coin featured the motto “Vires in numeris” (strength in numbers) on one side and a hologram on the other concealing a private key for accessing the “real” (digital) bitcoin.
What is a portfolio?
To get started in the world of cryptocurrencies, you will need an electronic portfolio, also known as a wallet.
Wallets are devices or software used for sending and receiving cryptocurrency.
Each wallet has:
- a public key, i.e. your address, similar to bank details. The key enables you to receive transfers
- a private key, i.e. your password, required for accessing your currency and making transactions.
If you lose your private key:
- In a private blockchain: if the key is conserved by the platform, you can generally ask for your password to be regenerated, as with any remote access system. However, if you keep your wallet off-platform, there is no way to recover it.
- In a private blockchain, in general the blockchain “giant” is able to regenerate tokens and return them where necessary.
How to choose a portfolio?
There are two main categories of portfolio: “hot” and “cold”.
“Hot” portfolios
These portfolios are connected to the web during use. They are easy to access, fast and practical, and can be used via a computer or smartphone, which means they are intended for regular transactions. But as they are connected to the internet, they are susceptible to hacks.
“Cold” portfolios
With these portfolios, your private key is stored offline. Your key may be stored on a memory stick or a simple piece of paper. Or you may have copied your key on a printed piece of paper on which the key takes the form of a QR code. Your key can also be stored on software on your desktop off-line, or on any independent peripheral device designed for storing your private keys offline.
As these portfolios are not connected to the internet, they may not be hacked and thus offer extra security. They are mainly intended for people seeking to conserve currency over a long period of time and for large quantities of digital assets.
With a portfolio, you can make and receive cryptocurrency transfers via blockchain technology.
Example of a “paper” wallet:
The following is included: your public key, which, to recap, enables you to receive bitcoins in your portfolio.
And your private key, used to access the bitcoins in your portfolio.
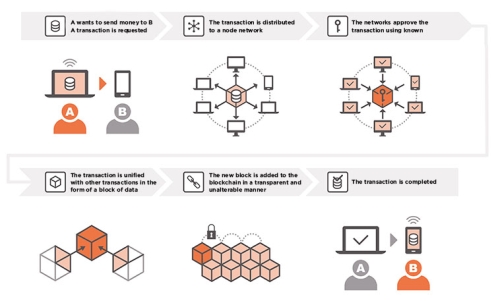
To fully understand the process, let’s take the example of someone looking to send money to someone else:
As a reminder,
- when cryptocurrency is used, it creates what we call a “transaction”.
- This transaction needs to be validated by people known as “miners”.
Prerequisite: the sender and the recipient must both have portfolios.
Did you know? You can check all the transactions made in the blockchain on the following website: https://www.blockchain.com/explorer?view=btc
Cryptocurrencies are not without risk
Market volatility
As discussed earlier, because bitcoin is based on a non-regulated market, its value depends entirely on supply and demand. As a result, the price can vary both upwards and downwards. And these movements can occur in relatively short periods of time. This strong volatility makes it a risky market.
As the currency does not have legal-tender status, when the value of bitcoin falls, central banks cannot intervene as they do with, say, the euro. As such, you need to be fully aware that you can incur losses as easily as you can make gains.
Tip: Invest only that which you are willing to lose.
Technological risks and legal/fraud risks
As described earlier, “hot” portfolios are risky because they are connected to the internet. Which means that they can be hacked.
Example of a hack resulting from “hot” portfolio security flaws:
In January 2018, a total of $530 million in cryptocurrency disappeared from the CoinCheck trading platform. The Mt Gox platform lost some $487 million following two hacks in 2011 and 2014.
In addition, fake trading platforms and fake cryptocurrency portfolios also exist. Lacking a legal status and regulatory framework, virtual currencies offer no guarantees. In the event of fraud, no compensation is possible, unless you take out a special insurance policy.
Tip: Always check that the company you use is approved as a payment institution by the Autorité de Contrôle Prudentiel et de Résolution (ACPR) as per Article L. 522-6 of the French Monetary and Financial Code.
***
- new uses of the blockchain
- Crédit Agricole trials blockchain technology for cross-border transfers

![[image] Table hashage en - credit agricole bank and group france [image] Table hashage en - credit agricole bank and group france](https://www.credit-agricole.com/var/ca/storage/images/_aliases/large/files/nouveau-site/images/image-tableau-hashage-en/4946074-1-eng-GB/99e2dab2b545-image-tableau-hashage-en.png)
![[image] The merkle tree hashing - credit agricole bank and group france [image] The merkle tree hashing - credit agricole bank and group france](https://www.credit-agricole.com/var/ca/storage/images/_aliases/medium/files/nouveau-site/images/image-the-merkle-tree/4946087-1-eng-GB/91f37a52217b-image-the-merkle-tree.png)